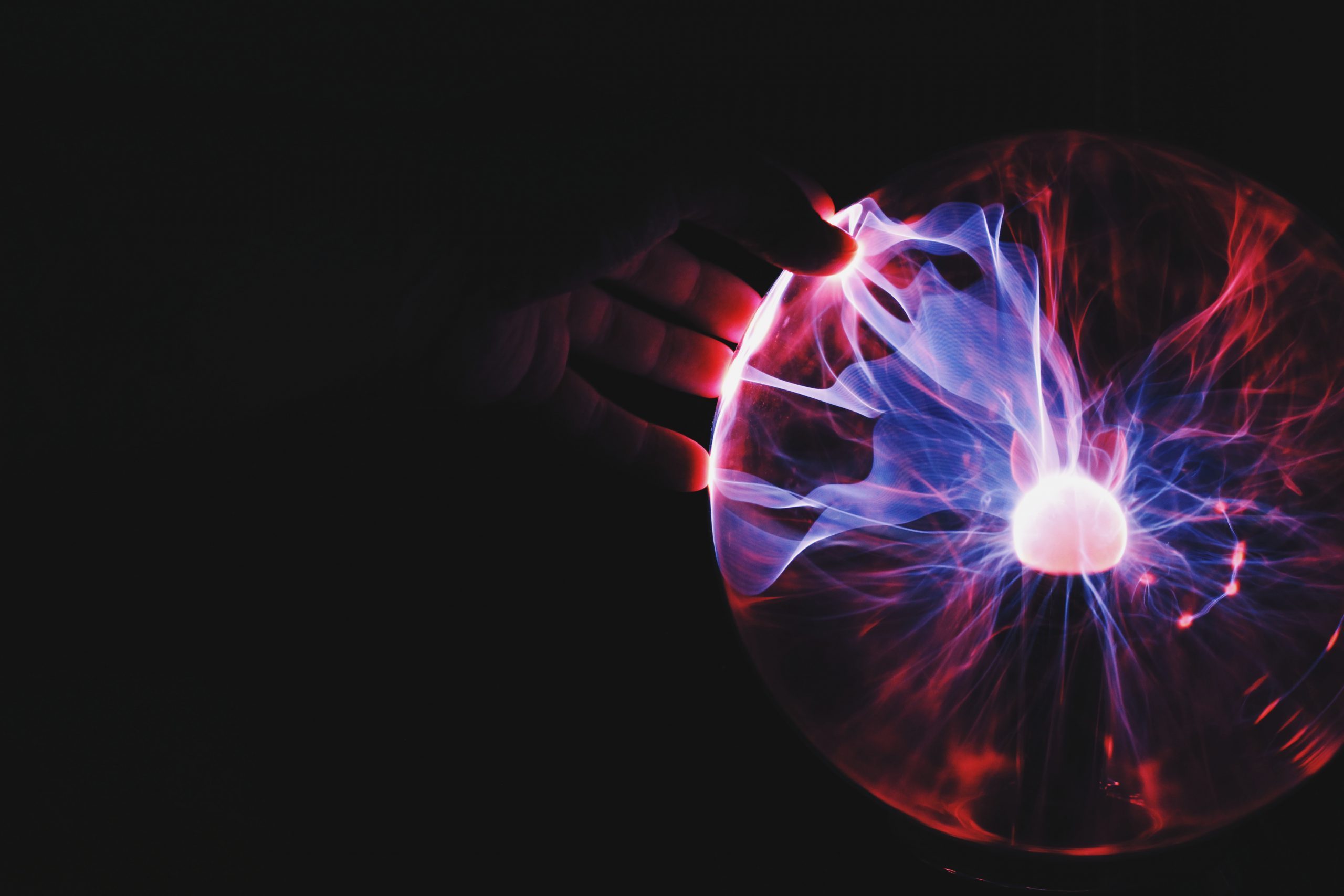
Security Testing: Protecting your valuable data and reputation
We live in a time when the world is extraordinarily well-connected, ever since the advent of the Internet. With rapid breakthroughs in Internet technology, data travels across the world at lightning fast speed. With the transfer of data — even sensitive data — made possible with just a few rapid key strokes, ensuring the sanctity and security of data is important not just for individuals, but also the organisations they trust their information with. With businesses expanding across geographies, seamless operations require that data is available to all teams across the world, simultaneously. While making data available to everyone improves ease of business, it also makes data more vulnerable to hackers who seek to steal sensitive and valuable information — like credit card details, bank account numbers, passwords, etc. In addition to this, an increasing number of business transactions are undertaken by users on mobile applications and public networks, further compromising the security of personal and financial credentials. Data breaches can cause permanent damage to an organisation’s reputation, and, ultimately, revenues, due to irreversible and permanent loss of trust from its customers. Due to all these reasons, businesses are beginning to invest heavily in systems that will help them protect sensitive information. Robust security testing is one of the most effective ways to achieve this.
Security testing refers to all the testing initiatives and activities undertaken by an organisation to ensure that their application is functioning seamlessly and without glitches or threats that may compromise the security of its customers’ valuable data, even before the application has been released. So in essence, it means all the tests that an application is put through in a production environment to gauge its functionality in the real world. During security testing, an application is tested for various key security parameters such as the possibility of data corruption, confidentiality, veracity, threat of exposure, stability, and uninterrupted progression. During security testing, information is tested across every layer within all the infrastructure, databases, networks and access channels of the application. When such robust efforts are made to ensure that customer data is secure, it adds to the overall quality and sound functioning of the application in question.
Largely, security testing falls under three major categories: web application security testing, mobile application testing, and networks and system testing.
In all three testing suits, to begin with, applications, networks and systems are assessed to pinpoint all the vulnerabilities indicated by the Open Web Application Security Project (OWASP) standard and other widely recognised and accepted frameworks. Initially, the applications, systems and networks are profiled by listing possible user entry points, understanding the security infrastructure already being used by the application, shared interfaces with other applications, the flow of data across layers with different boundaries, security clearances, data privileges, trust levels, and data breach threats. Once the profiling is done, a clear picture of how vulnerable the application, network or system is, is determined. Manual assessment is carried out in conjunction with automated scripts to identify threats that were missed by automated tools. And finally, there is reporting, assessment and mitigation of all the security threats can be exploited within the application, network, or system being targeted.
It is undeniable that in today’s technological landscape, security threats for sensitive applications have grown both in number and in magnitude. The impact of gaps in security with regard to sensitive information can bring even large companies to its knees. In such a scenario, robust and regular security audits are the only way organisations can survive. In addition to preventing accidental or unauthorised usage, security testing ensures that organisations are in compliance with security regulations mandated by regulatory bodies across the world — a factor that is doubly important for those that seek to expand or continue operations across geographies.